Companies that have chosen to entrust us with the protection of their business data





Easy to use, total control
Since 2011, we’ve been developing cybersecurity software in Italy that combines data encryption and usability, for those who want to work smoothly without giving up total control. Whether working in the cloud, on-premises, or on the go, we protect every piece of data continuously and compliantly, supporting those who work with a solid, flexible, and integrated approach designed to ensure peace of mind and operational continuity. Every aspect of your operations remains safe, under control, and accessible only to those you choose: everything you need to work securely is here.
Advanced encryption, real security
We apply encryption to sensitive data using end-to-end protocols and zero trust policies, ensuring no data leaves your perimeter.
Complete control
With boolebox you can protect business files, set custom access rules, track every change, and revoke permissions at any time.
Italian technology, international standards
Developed in Italy and compliant with ISO 9001, ISO 27001, and the Common Criteria standard, our data protection software is designed to meet the needs of the most demanding organizations.
A single platform for data protection, all the security you need.
Security Suite boolebox
Everything you need for the security of your business data, in a single dashboard.
Our boolebox Security Suite consists of 4 standalone solutions that allow you to protect your business data according to your actual needs, in a complete way.
Secure File Manager
Upload, organize, and share files securely, with real-time collaborative editing on Office documents, always protected.
Discover this solution >Secure E-Mail
Send and receive protected messages and attachments thanks to data encryption, with the highest level of security.
Discover this solution >Secure Password
Store and manage business credentials in a secure, encrypted, centralized vault.
Discover this solution >Secure Transfer
Share large files with advanced protection and traceability.
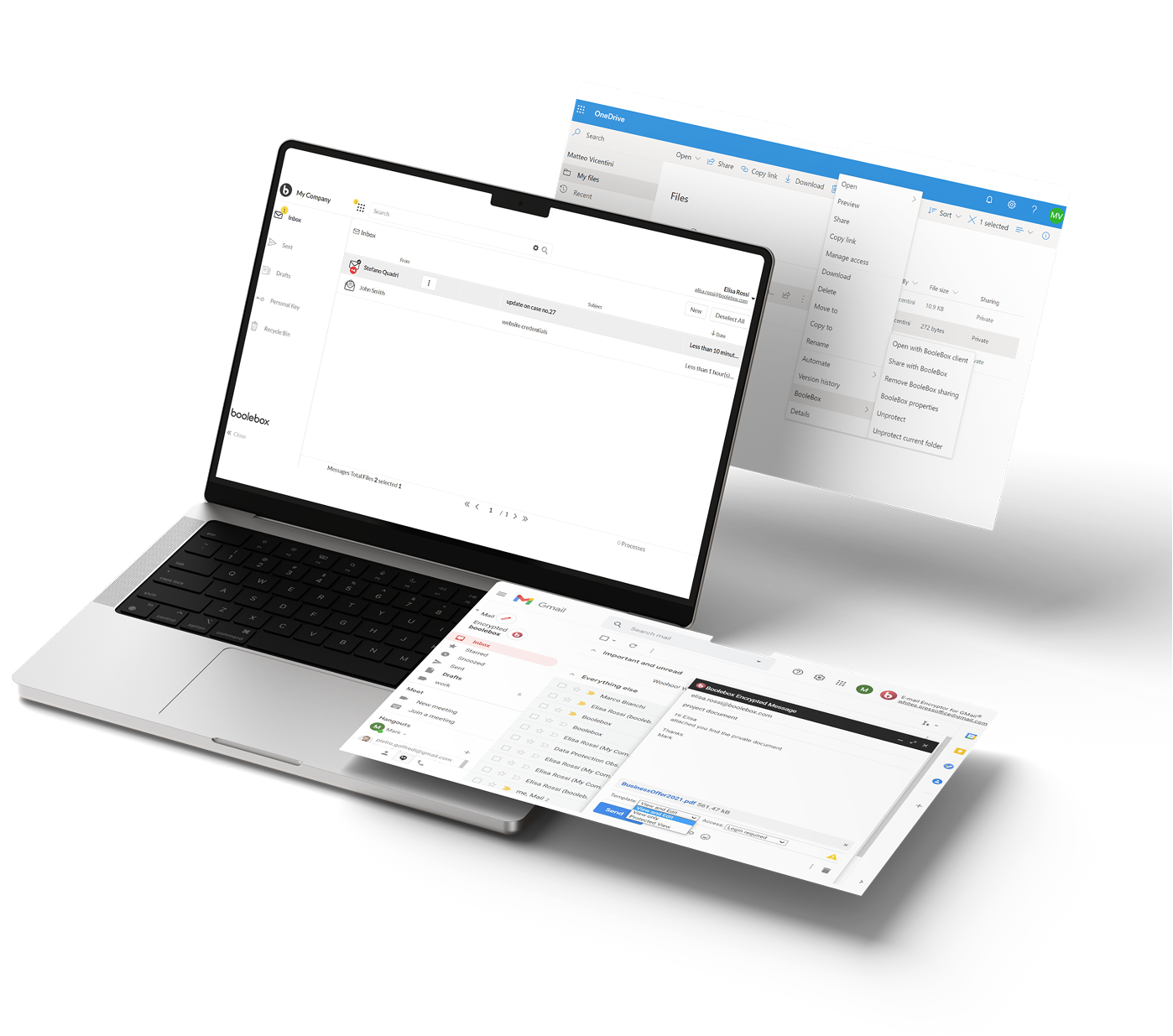
Discover this solution >Encryption Suite boolebox
Protect your company’s data even on external platforms
With boolebox’s Encryption Suite, you can encrypt sensitive business data without changing your way of working, because you protect files, emails, and attachments directly on third-party platforms like Windows, Outlook, OneDrive, and SharePoint. Our encryption technology, compliant with major security standards, helps companies ensure GDPR compliance and data protection both locally and in the cloud.
File Encryptor for Windows
Protect your business files locally while working in Office, in a secure environment that simplifies work for authorized users.
Discover this solution >File Encryptor for OneDrive & Sharepoint
Encrypt files and documents uploaded to Microsoft cloud with an extra layer of security.
Discover this solution >E-Mail Encryptor for Outlook
Apply advanced encryption to Outlook communications, maintaining full compatibility and traceability.
Discover this solution >Protect your company’s data wherever and however you want.
Same security, on all your devices
No matter where your files are: with boolebox you can manage business data protection locally, in the cloud, or in hybrid environments, always maintaining the same level of control.
Each module of the suite is designed to ensure operational continuity and file encryption, even when working remotely
On-Premises
Protect your data directly on your servers, maintaining full management autonomy
Cloud
Work flexibly and ensure encryption of every type of file in the cloud with the same effectiveness as local.
Hybrid
Combine both modes for a tailored security strategy, perfect for distributed or transitioning companies.
All the security you need:
boolebox data encryption, for your industry.
Different activities, same need: protecting sensitive business data.
boolebox is the right choice for companies and organizations that want to preserve confidential information and ensure business file encryption even in complex contexts.
Banks and Financial Institutions
To ensure business data protection locally and in the cloud, with advanced traceability and access control.
Read more >Law Firms and Consultants
To encrypt and protect documents, manage authorizations, share files securely, and archive them in encrypted form.
Read more >Public and Private Healthcare
To securely store diagnoses, reports, and clinical data in compliance with current regulations (GDPR and NIS2).
Read more >Public Administration and Institutions
To collaborate in protected and compliant environments, safeguarding citizen privacy and sensitive document security.
Read more >SMEs
All the most suitable encryption solutions to prevent cyber risks and loss of critical data.
Read more >Freelancers
All the most suitable encryption solutions to prevent cyber risks and loss of critical data.
Read more >Everything you need to know about data protection.

NIS2 in Practice: An Operational Checklist to Comply Without Slowing Down the Business
Over the past few months, we’ve talked extensively about NIS2: what it requires, which sectors are affected, and why it represents a major shift in the way security is managed. The picture is now clear: the directive is no longer a topic reserved for specialists—it is a concrete requirement that impacts processes, suppliers, and management responsibilities
13 Apr

Shadow IT: What Is Shadow IT? Causes, Risks, and Solutions for Companies
Shadow IT—meaning the unauthorized use of digital technologies within an organization—refers to employees or teams utilizing tools such as software, cloud applications, personal devices, or online services without prior approval or oversight from the IT department. This phenomenon is not necessarily driven by malicious intent; it often arises from genuine operational needs, such as the…
02 Oct

Credential Stuffing: How to Protect Corporate Credentials from Brute-Force Attacks
What is Credential Stuffing and Why is it a Threat to Companies? Credential stuffing is a cyber attack technique where cybercriminals use combinations of usernames and passwords stolen from previous data breaches to try to access other systems or applications. This type of attack affects both private users and companies, but it is particularly critical…
08 Sep
Boolebox: the software that protects every piece of data, wherever it is
We know that every day your company handles a huge amount of confidential information. Protecting this data means not only ensuring operational continuity but also safeguarding the trust that clients, partners, and employees place in you.
This awareness is what gave rise to boolebox, a security suite developed entirely in Italy, designed to integrate discreetly and effectively into business processes while respecting international standards.
The boolebox suite is designed to support you in complying with GDPR and NIS2 regulations, while also meeting the security requirements of international standards such as Common Criteria and ISO/IEC 27001 certifications.
With boolebox, business file encryption, data protection, and secure sharing become an integral part of daily work, without changing your tools or habits. Protect sensitive files wherever they are — locally, in the cloud, or on collaborative platforms — always maintaining full control.
The suite integrates advanced tools for data encryption, granular access management, and complete activity traceability. Its features cover every need, allowing you, for example, to encrypt and securely share business data even on Outlook, SharePoint, OneDrive, and other environments..
When you know you’re protected, you work with more freedom and efficiency: with boolebox, you can do it every day.